Posted
Alternate titles:
- “Diamonds are a Sith’s best friend”
- “I used to Bullseye Womp Rats in my t-shirt back home.”
- “That’s no Shamoon…it’s a space station attack!
Those of you who know ThreatConnect well are aware that we’re Star Wars fans. A recent example and awesome webinar if you haven’t seen it – The Need for an Evolved Threat Intel Lifecycle Webinar – involves the Battle of Hoth. You’ll also know that we tend to geek out on deconstructing security incidents.
Back in 2015, in the event planning leading up to Black Hat, our Marketing team came up with the great idea to create Star Wars-themed t-shirts for our 3rd annual BH/DC bash. Someone further refined that idea to incorporate the Diamond Model for Intrusion Analysis on the back, which made it an insanely great idea and kicked off a spontaneous multi-day nerdfest in our office. There are pictures, but since the Internet never forgets we didn’t share them to spare the dignity of those involved.
The Diamond Model is an approach to conducting intelligence on network intrusion events. The model gets its name (and shape) from the four core interconnected elements that comprise any event – Adversary, Infrastructure, Capability, and Victim.
Thus, analyzing security incidents (or intrusions/activity threads/campaigns/etc) essentially involves piecing together “the Diamond” using bits of information collected about these four facets to understand the threat in its full and proper context.
Star Wars provides a wealth of incidents for study – in fact, the entire story of Episode 4: A New Hope centers around the response to and consequences of a data breach. The climactic event in the movie, however, is of course the destruction of the first Death Star. Watching the movie with your cybersecurity glasses on gives a different perspective and raises many interesting questions. Why didn’t Vader recognize R2-D2 as the likely storage mechanism for the stolen plans? Why did the response team descend into bickering over ancient religions and eventual force-choking rather than dealing rationally and cooperatively with the situation? If they were such a critical external-facing vulnerability, why weren’t the Death Star’s exhaust ports better protected? That last one is the thread we decided to pull on and weave into the best con t-shirt this side of the galaxy. Seriously, we still have people mention that one to us at conferences eight years later!
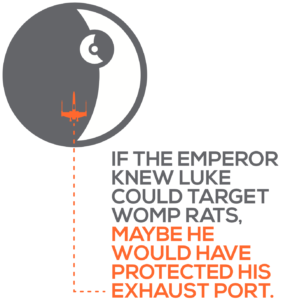
It isn’t hard to imagine that if the Emperor had known Luke could bullseye womp rats in his T-16 back home on Tatooine, he might have surmised that he could also nail small exhaust ports from his much more capable X-Wing with the help of the Force. But he apparently didn’t know that, which constitutes a major intelligence failure on behalf of the Empire that turned the tide of the war. The Empire would strike back, of course, but the inevitable return of the Jedi was set in motion. Had the Diamond Model been invented a long time ago in a galaxy far, far away, the outcome might have been different.
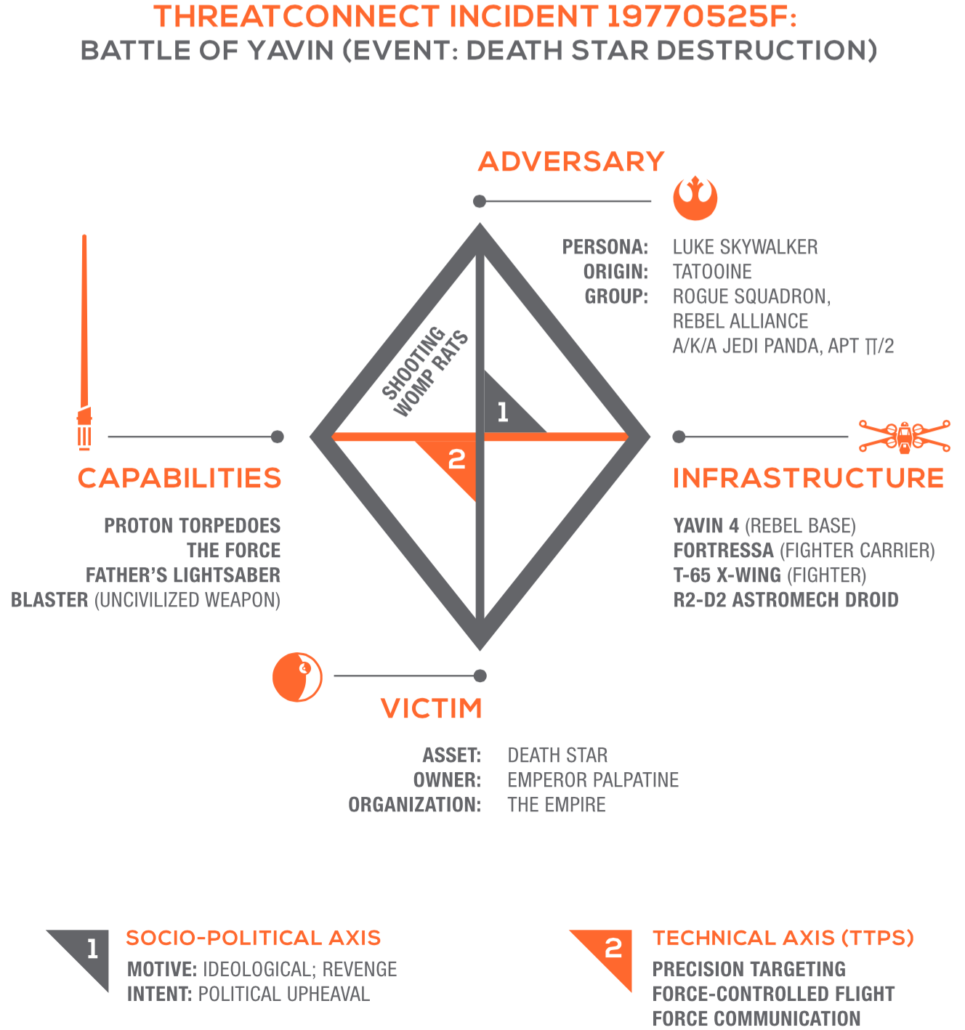
The graphic shows what the Empire could have reasonably known by assimilating the intelligence available to it at the time. The name of the incident underscores one of the pesky difficulties of incident analysis – dating. All we know of the earth-date of the incident is that it occurred “a long time ago.” We could go with the date of 0 BBY based on the Galactic Standard Calendar, but that has no relevance to earthlings. Thus, we’ve adopted the day the incident became publicly known – May 25, 1977 (which also happens to be the birthday of a certain kid I know named Luke, but I digress). “F” simply designates it as the 6th major incident of the day.
 We need not spend much time on the Victim element of the Diamond; the Empire understood the power and value of its critical asset, the Death Star. And their reaction to the theft of the plans implies that they knew about the risk exposed by the exhaust port vulnerability, but apparently underestimated the adversary’s means of exploiting it.
We need not spend much time on the Victim element of the Diamond; the Empire understood the power and value of its critical asset, the Death Star. And their reaction to the theft of the plans implies that they knew about the risk exposed by the exhaust port vulnerability, but apparently underestimated the adversary’s means of exploiting it.
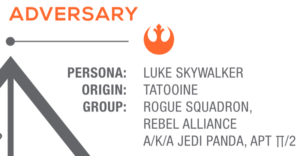 From what can be gleaned from the movie, the Empire had decent intel on a key adversary persona, the young Skywalker. Enough, at least, to get a proper geolocation (thanks to his OPSEC failure of taking rooted machines home) and murder his known associates (of course, this should have tipped them off to the whole Anakin connection much earlier, but we won’t go down that rabbit hole right now). They also had pretty good knowledge of the Rebel Alliance, but were hampered by fuzzy attribution and their somewhat amorphous structure. Certain imperial units tried to genericize references to the Alliance by using “APT Π/2,” while others emphasized the Force connection with the “Jedi Panda” moniker. We believe these naming inconsistencies led to confusion that effectively afforded the Alliance enough obscurity to continue offensive operations.
From what can be gleaned from the movie, the Empire had decent intel on a key adversary persona, the young Skywalker. Enough, at least, to get a proper geolocation (thanks to his OPSEC failure of taking rooted machines home) and murder his known associates (of course, this should have tipped them off to the whole Anakin connection much earlier, but we won’t go down that rabbit hole right now). They also had pretty good knowledge of the Rebel Alliance, but were hampered by fuzzy attribution and their somewhat amorphous structure. Certain imperial units tried to genericize references to the Alliance by using “APT Π/2,” while others emphasized the Force connection with the “Jedi Panda” moniker. We believe these naming inconsistencies led to confusion that effectively afforded the Alliance enough obscurity to continue offensive operations.
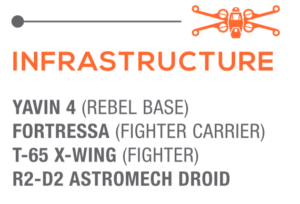 We must assume the Empire had a high degree of knowledge about the Rebel infrastructure involved in the attack. They slyly allowed the Millennium Falcon to escape the Death Star and tracked it back to the Rebel base on Yavin 4. As they moved to execute the takedown operation, they undoubtedly knew of the Rebel’s carrier and fighter class ships, evidenced by the fact that they neutralized nearly all of them fairly quickly. It is likely, however, that the Empire did not realize that the Alliance had commandeered an astromech droid that had once belonged to one of its top military officials. The failure to contextualize this small piece of intelligence would later prove costly.
We must assume the Empire had a high degree of knowledge about the Rebel infrastructure involved in the attack. They slyly allowed the Millennium Falcon to escape the Death Star and tracked it back to the Rebel base on Yavin 4. As they moved to execute the takedown operation, they undoubtedly knew of the Rebel’s carrier and fighter class ships, evidenced by the fact that they neutralized nearly all of them fairly quickly. It is likely, however, that the Empire did not realize that the Alliance had commandeered an astromech droid that had once belonged to one of its top military officials. The failure to contextualize this small piece of intelligence would later prove costly.
 And that brings us to the final element in the Diamond Model, Capability. They knew the Alliance fighters could deploy proton torpedoes. Led by two Sith, they certainly knew about the Force. They knew about lightsabers and – even though they couldn’t hit anything with them – they knew about blasters too. No serious intelligence gaps here.
And that brings us to the final element in the Diamond Model, Capability. They knew the Alliance fighters could deploy proton torpedoes. Led by two Sith, they certainly knew about the Force. They knew about lightsabers and – even though they couldn’t hit anything with them – they knew about blasters too. No serious intelligence gaps here.
While the Empire was missing key bits of information on some facets of the Diamond, their inability to make connections between the facets is what, quite literally, killed them in the end. The vertices between the points tie everything together and give the critical understanding of what the adversary wants and what they can do to accomplish it. In this light, it’s clear that they failed to grasp the sum total of Luke’s desire to revenge the death of his father (sssshhhh – remember he doesn’t yet know), his natural precision targeting ability, his inherent strength in the Force, his covert channel communication with dead-but-still-alive ex-imperial generals, etc. Had they been able to put all this together, the story might have ended differently. Sure, we would probably have missed the awesomeness of The Empire Strikes Back, but we could have skipped all that screen time devoted to the Ewoks as part of the attack on the second Death Star.
At this point, it should be obvious that the Empire needed a Threat Intelligence Operations Platform. If you’d like to learn more about our TI Ops Platform, reach out to one of our experts to learn more and get a personalized demo.